Your “application for unemployment benefits has been approved,” stated the letter from the Illinois unemployment bureau a few weeks back. That was perplexing, since I never applied and wasn’t unemployed. So I immediately told my (part-time) employer and the state unemployment agency.
Turns out somebody had stolen my personal information – again. [Insert grimace emoji here.]
I wasn’t alone. Fraudulent jobless claims are a rampant scam across the country that accelerated during the COVID crisis as jobless benefits increased. More than a third of a million people in my state alone were also victims of the scam, including several people I knew. Although national tallies are still under way, the unemployment fraud is massive: California estimates more than $11 billion was stolen. All told, tens of millions of people could’ve been scammed in this way.
Since this was the third time I’d been a victim of identity theft and fraud, I was steamed and wanted to know how thieves kept getting my information and conducted their grifting. If I knew where they got my information, maybe I could change some of my online behavior or take better precautions. I spent a lot of time on the phone giving my state unemployment agency my details. They were so swamped, it took them weeks to get back to me after I left a voicemail reporting the fraud.
I realized I would have to take matters into my own hands. This led to a month-long odyssey that included interviews with security experts and law enforcement officials and some frightening insights about the modern thieves market called the dark web. It was also a dispiriting trek as I was reminded how helpless we can be in the face of global technology that makes life easier for both the law abiding and the criminal.
I don’t consider myself an easy mark, although I’m certainly not an expert on cybersecurity. As a financial reporter and experienced identity theft victim, I take almost every precaution. My credit files with the three major credit reporting firms have been frozen for more than a year (triggered by an unrelated scam). I use a search engine that doesn’t track or store queries. I regularly sweep my computer for viruses and I send all financial information via secure fax instead of vulnerable email. My spam filters are pretty diligent. I even leave my fax machine hooked up to my only landline to frustrate frequent robo-callers. I don’t even open video links sent by friends. Still, like any online consumer, once I pass personal information to a third party, I can’t bring it back.
This caution helps protect me from the efforts of cybercriminals to exploit the growing number of workers online by increasing their attacks through “phishing” (stealing information through email inquiries).
Related: Protecting Yourself and Your Data
Unfortunately, we are not the only ones in possession of our key pieces of information, from our date of birth and Social Security numbers to banking and credit card numbers. Like most people who do nearly all of their work, shopping and communications on the web or through email, I know I compromise my privacy on a daily basis. Every time I do an online transaction, search or register on a Web site, some entity on the other end has my important personal information. Information is valuable currency these days; my data is used to market me more stuff every time I log on. In most cases, I had to trust that vendors’ cybersecurity systems were robust. I try to be careful, but I know I really have no control over my data once it leaves my keyboard and flows into cyberspace.
Data breaches, instances where digital information is stolen by outside actors, are at an all-time high. Last year, more than 737 million data files were ripped off, according to hacked.com, which described last year’s digital pilferage as “a digital pandemic.” With millions working remotely on their computers during the pandemic, the FBI recorded a 400% increase of cybercrime reports. The recent mega-hack of corporate and government systems, suspected to be conducted by Russian intelligence operatives, is a case in point.
Sometimes hackers want to mess up or shut down government or corporate systems or just want to see if they can break in. It’s a challenge. It’s their version of triathlons. But the vast majority of breaches are pure theft – that’s where the money is – to quote bank robber Willie Sutton. The Verizon 2020 Data Breach Investigations Report, which analyzed more than 32,000 security incidents across the globe, found that “86% of the data breaches were for financial gain – up from 71% in 2019.” Government and corporate and other data-rich systems like health care databases are prime targets. Lately they’ve been raiding school districts and municipal systems.
Thieves probably snagged the identifying details used to file my bogus unemployment claim from one such data breach. I know from sorry experience how they do it. But tracking down who stole the data – and getting it back – is not easy. It helps to know where your information was stolen from: Data breaches are usually made public, although there are tens of thousands of them. The range of systems being compromised is vast – from Target to the giant credit file company Equifax. A West African fraud ring, for example, reportedly used data stolen in the Experian breach to steal more identities.
According to Edward Garb, a security researcher at Atlas VPN, a digital privacy company, “finding out the company that breached your data is the easy part. Now, you need to explore the dark web to find a vendor who sells records from that data breach. This might or might not be possible.”
My next step was clear: I had to scour the dark web to try and retrieve and remove my information. But this was almost impossible.
The dark web is a section of the Internet that’s not accessible through conventional search engines. It’s a subterranean level of the Internet, something akin to a series of unlabeled subbasements. You have to know exactly where you’re going, although even then it’s not neatly indexed like the “surface” web. Sites on the darknet mostly have a “.onion” suffix, instead of “.com, .net, or .org” on the regular web.
“You can’t simply browse the darknet.” Garb adds. “You have to know what you are looking for. You must know the address of the website you want to access, or at least a place where you can find those addresses. To do so, people turn to Reddit or closed forums on the surface web. Probably the most famous place is Reddit’s darknet subforum, with more than 146,000 users.”
Complicating matters, I learned that having a dark web address only gets you to the front door; you need to be invited to a dark web site, which is accessible by specialized software such as the TOR browser, also known as an “onion router,” which makes searchers anonymous as they explore deeper layers of the web.
Not surprisingly, TOR, originally designed to hide the identities of government agents, was developed by the same Pentagon agency that developed the Internet (DARPA).
If the government designed and built the Internet and its wayward cousin the dark web, why can’t law enforcement agencies shut it down or at least grab a few major perpetrators? I put this question to Joe Koletar, a fraud expert and former Army intelligence officer. He also served for the FBI for 25 years.
“FBI has a lot of horsepower devoted to the digital world,” Koletar said. “But [the dark web is] distributed like a virus. There are too many small players. Any attempt to attack it, changes it.”
Koletar said that, like a lot of digital criminality, dark web data crooks are often paid in bitcoin, a digital currency. “Bitcoin is a terrorist, blackmailer or crook’s dream,” Koletar adds. “It can’t be traced and isn’t anchored in anything.”
Further frustrating law enforcement efforts to crack down on dark web stolen-data marketplaces is that the darknet is a grouping of websites that are not run by one entity. Communication occurs in private messaging and “most users use the TOR browser together with a virtual private network (VPN) service, which makes them completely untraceable, even to their Internet service provider or other third parties,” Garb adds.
“In short, it is hard to track down the criminals because the user’s IP address is hidden and changed, browsing data is encrypted, and they send and accept payments with bitcoins. The main idea of the darknet was obfuscating important information and identities, which it does extremely well, but cybercriminals found that it is a perfect place for them to trade illegal goods and services.”
When I prepared to search for my stolen information on the dark web, I asked a close friend who manages cybersecurity for a large company where I could look for the identity robbers who used my name to apply for jobless benefits.
He made some helpful suggestions – I should use TOR on a spare computer and set up a VPN to ensure privacy. He also warned me against the hunting expedition.
“Be extra careful, because as a known author, once you publish you are a target,” he advised. That made me rather squeamish since I didn’t want to become bait for a cyberattack. I do nearly all of my work online and my articles and email are posted in countless locations. Even though I have two backup computers, they are on the same network. If I wasn’t fully able to cloak my IP address – the signature for my network – I would be roadkill for any hacker. So I demurred on going any deeper with a dark web dive. I was way out of my league.
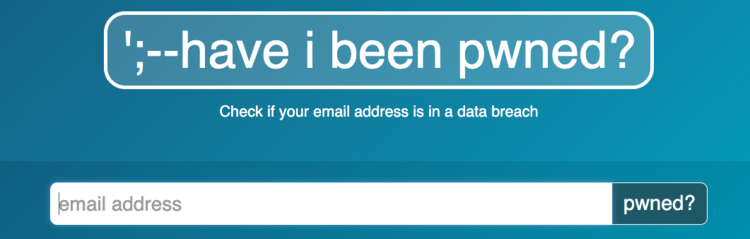
So much for my data search and rescue mission. Instead, I searched https://haveibeenpwned.com/ to see if my email had been “pawned.” The site, which provides imprecise information on data breaches where your information may have been stolen, confirmed that my email address was lifted. Of the 17 data breaches identified, one stood out: It was a site hit by a massive hack in 2014 (Forbes.com). All told, though, there was little more to do, since my email could’ve been in no less than 10 billion data files, the site noted. I also received notification from my browser security that some 200 passwords had been “compromised” on sites I visited.
My search left me feeling disappointed and exposed – protecting my identity and identifying the criminals seemed an impossible task. I was also confused.
About a week receiving the unemployment letter from my state, a debit card with my first week’s benefits arrived in the mail (which I shredded). It seemed puzzling. If you would go to the trouble of stealing a benefit with a card loaded with money, wouldn’t you send it to another address? But I was told it’s likely this set of thieves was just using me to probe the state computer system for weaknesses.
Once again, I was just a pawn in someone else’s game.





